Alright, here's a quick guide on how we were able to get SiteLock VPN working on my Raspberry Pi (and will probably work with any/all flavors of PI running a Debian kernel.)
Setup OpenVPN.
It starts off rather basic that every VPN asks you to do. Also this document assumes the server with Linux that you are logging into has 'sudo' rights set for the user that we will be executing commands for. This document also assumes that terminal is launched either via GUI or by default the moment you login to your Raspberry Pi.
sudo apt-get install openvpn unzip ca-certificates nano
Get the four packages:
- OpenVPN Package (it may ask for your user password again)
- Unzip utility in case your distro does not have that.
- CA-Certificates is already installed in most distros however this is nessecary to prevent any certificate trust errors when attempting to download the ovpn.zip files.
- Nano is a text editing software that we will be using for changing the vpn.ovpn file explained later in this documentation. Raspberry Pi disto's will more then likely have this installed already. You are more then welcome to use other editors such as "vi." however, for the sake of this documentation we will be using nano.
apt-get may report that you already have these (or all) files. If so then great we can move onto the next step.
cd /etc/openvpn
Lets go over to where openVPN will look for our files.
sudo wget https://anubianhost.com/account/downloads/ovpn.zip
This will grab the zip file off of the Anubianhost account and transfer it to your /etc/openvpn folder.
sudo unzip ovpn.zip
unzip the ovpn.zip files.
sudo rm ovpn.zip
Optional: you can delete these files once you are finished.
sudo openvpn vpn.ovpn
Launch the openvpn via command-line and afterwards it will ask for your credentials.
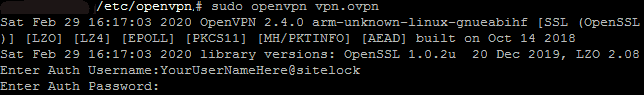
Username: YourUserNameHere@sitelock
Password: YourPasswordHere
It is important to have the @sitelock at the end of your username or else it will not register.
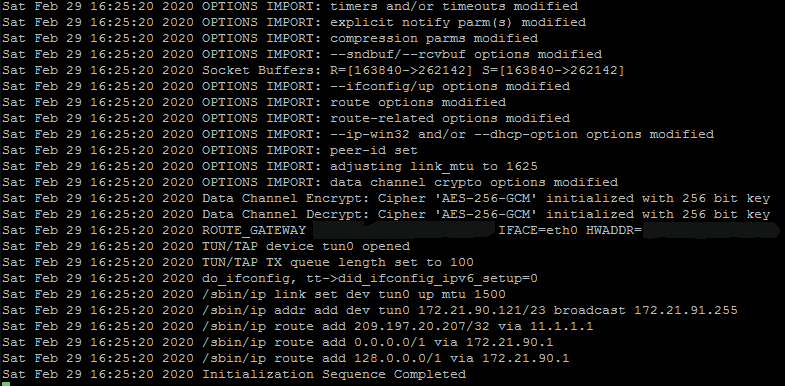
At this stage you can either minimize this window on your Raspberry Pi if you are running within a GUI environment. Or, if you are within shell you can either CTRL+ALT+F1 to choose a different shell session on Raspberry Pi (Raspberry Pi's have their GUI on CTRL+ALT+F2 and the original console on CTRL+ALT+F1, other linux variants have more function keys bound to consoles). Or, if you have the 'screen' application loaded and launched prior to openvpn you can simply press CTL+A and CTL+D to background OpenVPN within screen.
Changing servers.
Obviously as a Linux user you will want to choose the VPN closest to you for the fastest and best connection. Your provider should have given you a listing of servers that you can connect to. To perform this step type in the following.
sudo nano vpn.ovpn
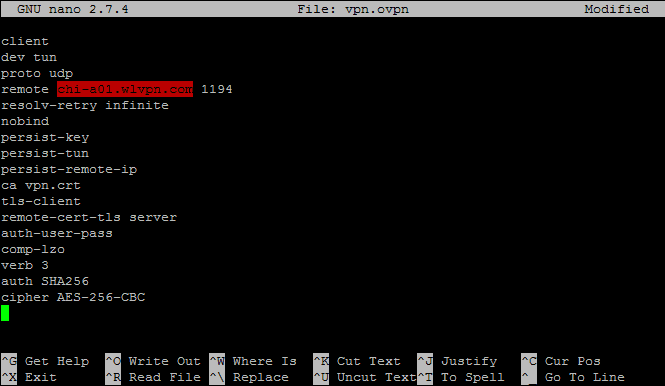
This contains your OpenVPN script:
client
dev tun
proto udp
remote chi-a01.wlvpn.com 1194
resolv-retry infinite
nobind
persist-key
persist-tun
persist-remote-ip
ca vpn.crt
tls-client
remote-cert-tls server
auth-user-pass
comp-lzo
verb 3
auth SHA256
cipher AES-256-CBC
The area that we highlighted in red is the section we will need to change to whatever server you wish. By default it's pointing to the VPN servers in Phoenix, New York (phx-a01.wlvpn.com) . In the example above we changed the server to Chicago, Illinois (chi-a01.wlvpn.com)
After you have modified this file. press Ctrl+X to exit
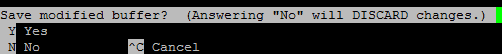
Press "Y" to save changes.
![]()
You can overwrite your existing vpn.ovpn file if you want. However, if you are moving around or traveling from state to state it may be a good idea to save it as a different name so that you can point your openvpn to whatever location you are at.
Troubleshooting:
This section covers some basic problems you may experience when using OpenVPN within a Linux terminal environment.
AUTH: Received control message: AUTH_FAILED:
![]()
This occurs if either the username or password has been entered incorrectly. Check the username and password and try again. Usernames and passwords within linux are case-sensitive. If this fails contact support to verify your username and password.
Cannot resolve host address:
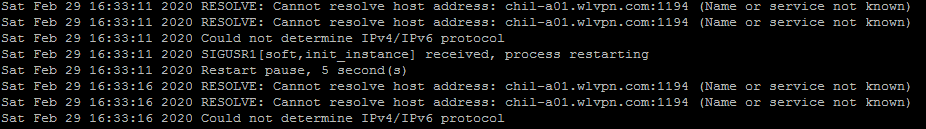
This happens if either the server does not exist or the server-name has been typed incorrectly. check your vpn.ovpn file and try again.
Notes on IPV6:
At the time of writing this document. IPV6 is not supported for VPN Tunneling and will have to be disabled so that all traffic goes through IPV4. In america IPV6 is still being rolled out and predominantly the most used standard is still IPV4. To disable IPV6 within Debian and Ubuntu is easy to accomplish.
sudo nano /etc/sysctl.conf
go to the end of the document and add the following:
net.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.disable_ipv6 = 1
net.ipv6.conf.lo.disable_ipv6 = 1
Save and reboot your Linux machine.
